Cyber Risk Assessments
Are you aware of what risks you are exposed to, or the risk assessments you are required to perform? What is the most cost-effective way of protecting your digital assets? At Zacco, we can assist you.
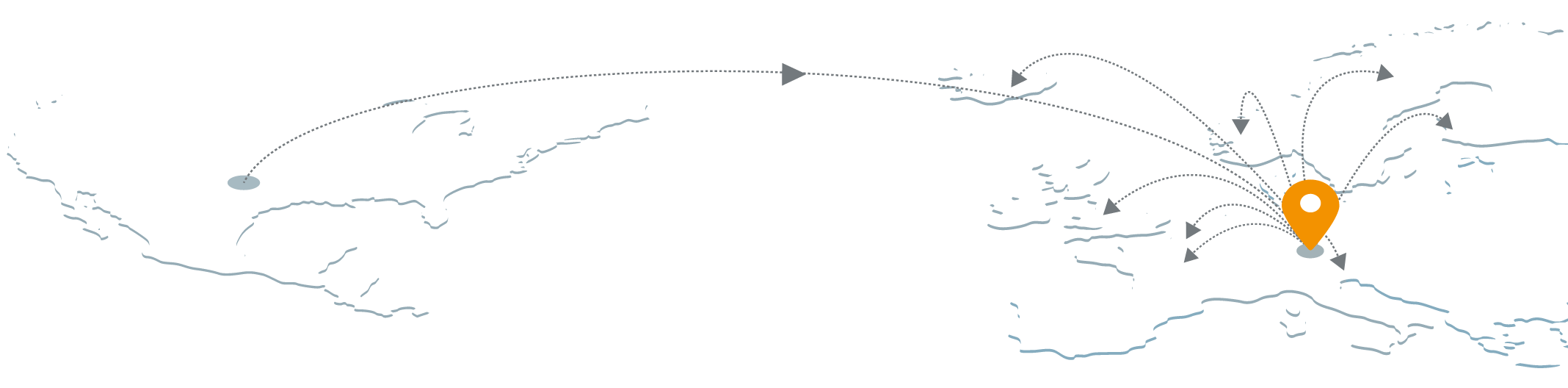
Cyber Security Risk assessment is the process of identifying, analysing and evaluating risk. The service ensures that the cyber security controls/capabilities you choose to implement are appropriate to the risks your organisation faces and accepts. Without a risk assessment to inform and quantify your cyber security choices, you could waste time and money in the wrong places for the wrong reasons, on risks that are unlikely to occur or will not affect your organisation.
Likewise, it is possible that you will underestimate or overlook risks that could cause significant damage. This is why so many best-practice frameworks, standards and laws – including the GDPR (General Data Protection Regulation) and DPA (Data Protection Act) 2018 – require risk assessments to be performed.
Cyber Security Risk Assessment helps you prioritise your efforts
First, a Cyber Security Risk Assessment identifies the various information assets that could be affected by a cyber-attack (such as hardware, systems, databases, applications, customer data and intellectual property), and then identifies the various risks that could affect those assets. Following this, we conduct a risk estimation and an evaluation, and then select the controls needed to treat the identified risks.
It is important to continually monitor and review the risk environment to detect any changes in the context of the organisation. We can help you maintain an overview of the complete risk management process.
Back to all services